Encryption - General Information
The Infoserver is able to apply advanced encryption methods on passwords and TCP communication (SSL). In the default configuration, only the password encryption is active, meaning that passwords saved in the Infoserver.ini and the database are encrypted as well as login-data submitted on the administration website. The default encryption-method is an RIJ (Rijndael/AES: symmetric encryption) algorithm with fixed key-length of 128 bit.
Additionally, it is possible to activate encrypted communications (SSL) for HTTP (Infoclient connections and administration website). Since SSL demands some sort of certification, the Infoserver can either create self-signed certificates or can use certificates issued by a certification authority.
Password Security
All admin and domain passwords used by the Infoserver are saved encrypted . Roles must use their domain password for logging in. The passwords of Roles are not saved in the Infoserver, but a compare-request is sent to the domain and a successfull login is only granted, if an "OK" is returned. The login in the administration interface is encrypted as well, meaning that the user-credentials are encrypted before sending them to the Infoserver.
The Admin passwords (Login & MailToInfo) as well as the password for access to the Native Domain are saved encrypted in the configuration file. The admin's password can only be decrypted by the Infoserver. The admin's password can be edited in the Infoserver administration website. For editing the admin's password please check the chapter Password.
In case the Infoserver admin password was lost or is unknown, then you can reset the password by changing the encrypted value back to the standard password of the admin (bestinformed) in the configuration-file Infoserver.ini and restarting the Cordaware_bestinformed_best_web service thereafter.
[general] password =K0jTn4NoAmsADGJlc3RpbmZvcm1lZGgDYQFhAWEB |
Passwords of the domain admins are saved encrypted in the Infoserver database and can only be decrypted by the Infoserver. These passwords can only be edited from the administration interface of the Infoserver. A reset in the database is only possible for those users, which have access to the database and the right to write to the appropriate table. Please note that tampering with any data in the database is at your own risk!
Therefore, passwords are saved and encrypted in the database. For the domain-administration, the user and his password can be set up in the domain solely for Cordaware bestinformed for avoiding the use of a productive user.
|
As of All-In-One version 6.4.1.6, you have the option to use settings for 2FA and Admin account locking. |
2FA - Two-Factor Authentication
You can verify the identity of users logging into the Cordaware bestinformed web interface using Two-Factor Authentication (2FA). This process utilizes the OTP (One-Time Password) method. Below you will find instructions for activation, user setup, and an overview of all configuration options.
1.Administrative Activation (Global)
The admin can activate 2FA in the app System > System (global) within the General section. Enable the checkbox Two-factor authentication: Active / Webinterface and click Save to apply the changes.
![]()
If this option is deactivated, two-factor authentication will be discontinued for all affected users.
|
If this option is disabled, 2FA will be deactivated for all affected users. Existing user secrets remain stored. If the feature is re-enabled, users must use their previously configured secrets. |
2.User Setup
Following global activation, each user can individually configure 2FA in their personal user settings:
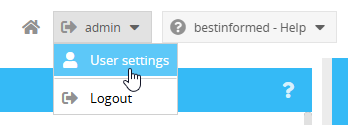
1.Navigate to your user settings.
2.Scan the provided QR code using a common authenticator app (e.g., Google Authenticator or Microsoft Authenticator).

Alternative: If scanning is not possible, you may copy the shared secret and enter it manually into the app.
|
Note Please ensure that the date and time on your mobile device (authenticator app) and the server are identical, since 2FA tokens are generated based on the current time (TOTP). Discrepancies can cause the codes to be rejected as invalid. |
3.For final activation, enter the six-digit One-Time Password (OTP) generated by the app into the web interface.
4.Following successful activation, a number of backup codes defined by the admin will be displayed. These serve as a security reserve to bypass or deactivate two-factor authentication if necessary.
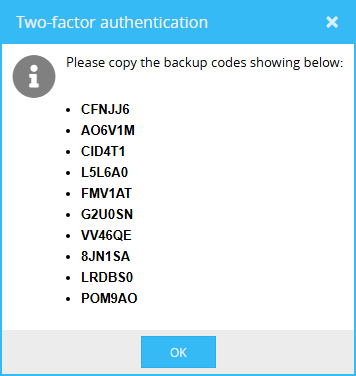
|
Please ensure that these codes are stored securely and protected from unauthorized access. You can generate new backup codes in your user settings at any time |
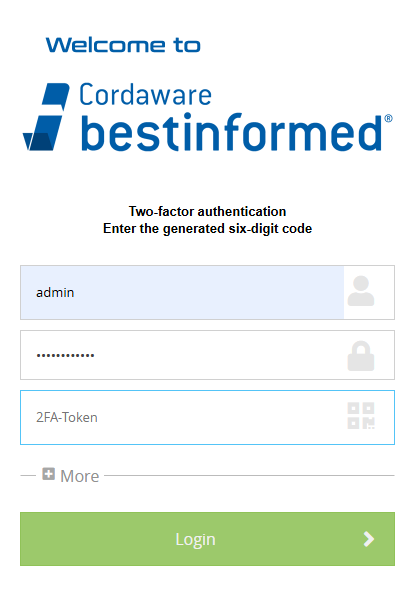
3.Login Process with Two-Factor Authentication
Following the successful activation of Two-Factor Authentication, you must provide the One-Time Password (OTP) from your authenticator app during every login process. The process is structured in two stages: first, the username and password are entered and confirmed. Only then will the input field for the 2FA token appear, where the current code from the app is entered to complete the login.
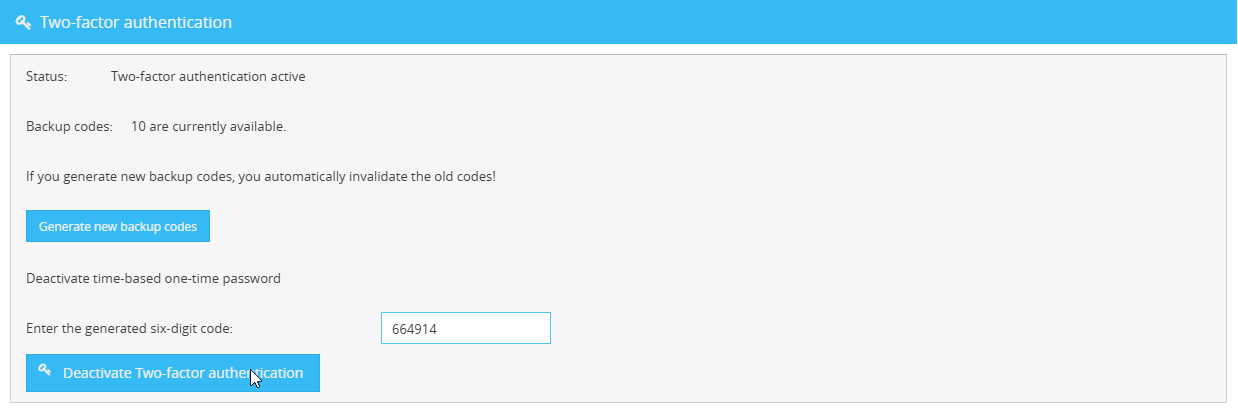
4.Deactivating Two-Factor Authentication
To deactivate Two-Factor Authentication, navigate to your user settings again. Enter your current One-Time Password (OTP) from the authenticator app or one of your backup codes. By clicking the Deactivate Two-factor authentication button, the function will be disabled for your account.
5.Deactivating Two-Factor Authentication (admin)
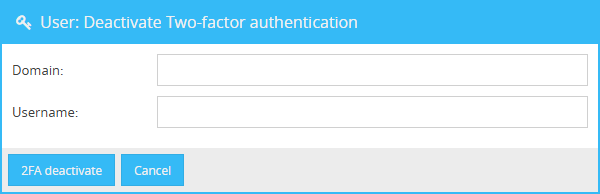
The admin has the option to deactivate Two-Factor Authentication (2FA) for users directly via the web interface. To do this, navigate to System (local) in the menu. From there, click the button "User: Deactivate Two-factor authentication" to open the deactivation form.
In this form, the admin specifies which account's 2FA should be disabled. Both the domain and the username must be entered. If the domain field is left blank, the default domain will be used.
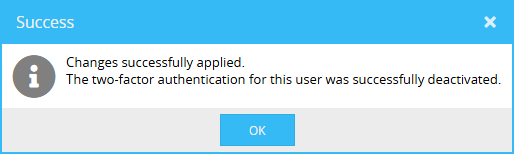
Once the deactivation is successful, the following confirmation will be displayed:
6.Administrative Settings
There are various settings available to modify Two-Factor Authentication. These settings can be configured in the Infoserver.ini. For further information regarding the Infoserver.ini, please refer to the Serverboard chapter.
Section |
Setting |
Default value/Example |
Function |
bi_auth |
2fa_backupcodes_count |
2fa_backupcodes_count = 10 (Default) |
This setting determines how many backup codes are generated for the user during the 2FA setup. |
bi_auth |
qrcode_alias |
qrcode_alias = |
By default, the entry in the authenticator app is displayed in the format bestinformed: User @ Server. This setting allows you to replace the server designation with a custom text. Without manual adjustment, the server's computer name is used automatically. |
Locking the Admin Account
You have the option to lock the admin account for a defined period after a specified number of failed login attempts. This measure significantly increases account security, as brute-force attacks are effectively prevented or hindered by the resulting time delay.
Configuration is managed via the following entries in the Infoserver.ini. Further information can be found in the Serverboard chapter.
Section |
Setting |
Default value/Example |
Function |
bi_auth |
admin_login_attempt_enabled |
admin_login_attempt_enabled = true/false (Default=false) |
This setting activates the locking of the admin account. After a change, the service Cordaware_bestinformed_best_web must be restarted. |
bi_auth |
admin_login_attempt_count |
admin_login_attempt_count = 5 (Default) |
Defines the number of permitted failed attempts before the account is locked. |
bi_auth |
admin_locked_timer |
admin_locked_timer= 30 (Default) |
Defines the duration of the lockout in minutes. Once expired, the admin_locked_count value is automatically reset. |
bi_auth |
admin_locked_since |
admin_locked_since = |
This entry shows a timestamp indicating when the admin account was locked. |
bi_auth |
admin_locked |
admin_locked = true/false (Default=false) |
Indicates the current lockout status of the admin account (true = locked). |
bi_auth |
admin_locked_count |
admin_locked_count = |
This value records the current number of failed login attempts. |
bi_auth |
admin_locked_reset |
admin_locked_reset = true / false (Default = false) |
If this setting is set to "true", the admin_locked_count counter will be reset automatically upon a successful admin login. |
bi_auth |
admin_locked_startclean |
admin_locked_startclean = true/false (Default=false) |
Determines whether the admin_locked_count should be reset after a restart of the web interface. |